THE FIRST VENDOR
INTELLIGENCE
PLATFORM
FOR GTM
Not quadrants. Not reviews. Not sponsored content. Runtime data that Security, Legal, Marketing, and Procurement can finally trust.
This data has never existed. Now it does.
THREAT HUNT REPORT 2025
Our comprehensive analysis of GTM stack surveillance infrastructure. Vendor behaviors, defeat devices, data exfiltration patterns.
DOWNLOAD NOWPDFThe Devil's Regex
Commercial Intelligence
Exfiltration Analysis
ZeroSense + DemonScript
We found five zero-day vulnerabilities in the 6sense/TrenDemon stack by visiting their privacy policy page with a HAR recorder. eval() RCE, supply chain compromise, and cross-customer PII leakage.
Video players are weaponized as execution triggers. When the video ends, eval(postCompletionScript) fires. TrenDemon SDK contains 6 distinct eval() vectors.
DEFEAT DEVICES
ID Resolution Scripts
Scripts designed to circumvent browser privacy controls. Reverse-engineer visitor identity without consent.
PRE-CONSENT EXFIL
Data Collection Before Opt-In
Data capture begins before consent banners appear. Behavioral tracking fires on page load.
VENDOR CHAINS
Hidden Data Flows
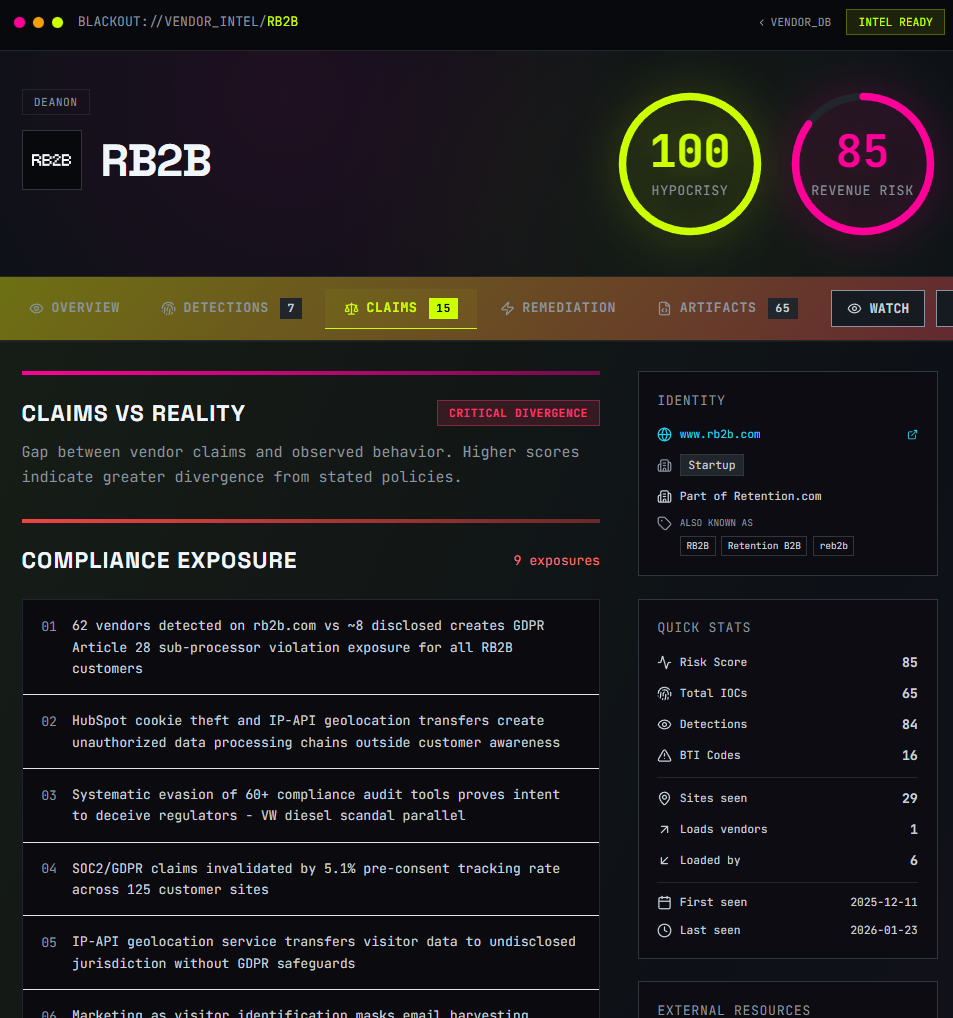
Undisclosed data sharing between marketing tools. Your "vendor" has vendors you don't know about.
THE GTM
KILL CHAIN
The step-by-step marketing campaign process maps 1:1 to the Lockheed Martin Cyber Kill Chain. This isn't a metaphor. It's a framework.
EXPLORE THE KILL CHAINYOUR GTM STACK IS A
LIABILITY
Your vendor's SOC 2 badge doesn't prove what their JavaScript does at runtime. We map what's running. We prove what it does. All from the outside.
SCAN YOUR SITE